Home
Inperium Sell
Two-Factor Authentication
Two-Factor Authentication
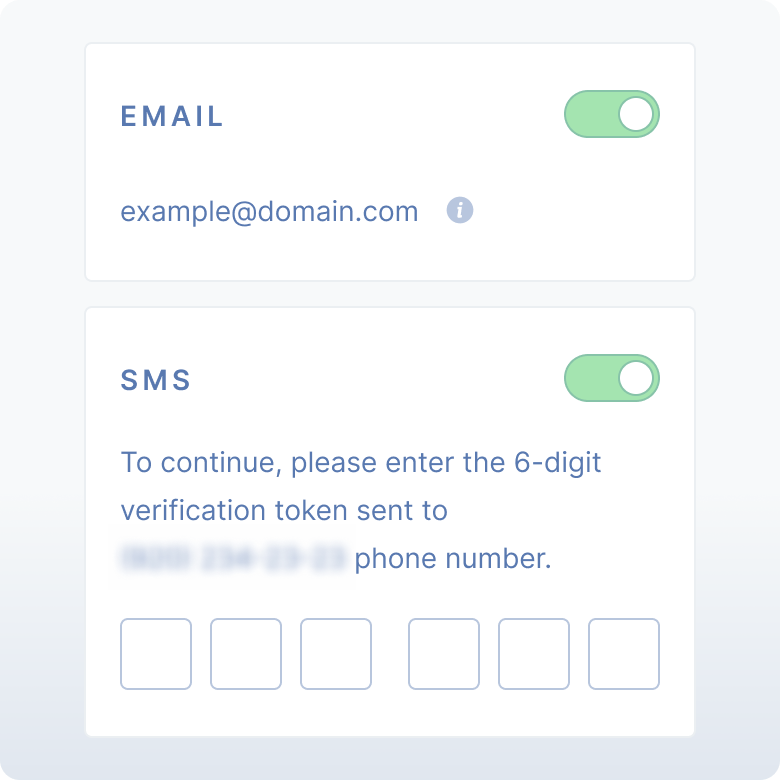
If you rely on passwords alone to control access to your systems and data, you’re putting your organization at serious risk of a costly breach. Today, most security experts recommend requiring two-factor authentication (2FA), which supplements the traditional password with a secret code sent to the user by SMS or email. Inperium Sell includes 2FA out of the box, enabling you to dramatically enhance the security of your sales data without imposing any significant burden on your staff.

Protect your business by keeping your data secure
Your CRM not only contains valuable data; it’s the sales and marketing hub for your IT ecosystem. Inperium Sell helps you keep intruders out of your systems by providing reliable 2FA. In addition to their username and password, users must enter a secret code sent to their phone or email. Hackers who steal or buy passwords are blocked at the door!

Pass compliance audits and avoid steep fines
Strong access control is a core requirement of most data protection regulations, including PCI DSS, SOX, GDPR and HIPAA. Taking advantage of the two-factor authentication built into Inperium Sell is an easy and effective way to comply with these stringent mandates, while also satisfying your own internal security policies.
Secure your CRM without extra expense or hassle
The two-factor authentication in Inperium Sell does not force you to purchase and learn any special tools, such as a code generator or an authentication app, nor does it require your users to carry special key fobs or other gadgets. Instead, it sends a verification code directly to the user’s phone number or email address. It’s convenient for them and cost effective for you.
Already using Inperium Sell and looking for additional information about this feature?
View Documentation

FAQ about Two-Factor Authentication
What is two-factor authentication?
Two-factor authentication is an effective method of strengthening access control to IT systems and data. With 2FA, users typically must enter their user ID and password, and the system will send them a one-time security code that they must enter within a certain period of time. This process renders stolen credentials useless to a would-be attacker.
Is two-factor authentication required?
Two-factor authentication is a globally recognized best practice for improving security. Many industry, country, state, and local data protection standards require strong access controls, and 2FA is a great way to satisfy those requirements and protect your data.
Can two-factor authentication be hacked?
It is possible to bypass 2FA, but it’s not easy. Attackers would need to not only somehow get your username and password, but also manage to intercept the verification code sent to your phone or email in time to enter it before it expires.
More Features Related to Two-Factor Authentication
Create Your Free Account
Try Inperium products for free for 10 days. You'll have all the features and receive full support during this trial period.